It is no secret any more that all modern CPUs released are affected to some extent by a serious issue because of their fundamental design of doing aggressive speculative execution. Specially malformed code can be used to steal the private data of other processes, including sensitive data like passwords, security keys and so on. In this article, we will see how to disable the Meltdown Fix on AMD CPUs After Installing KB4056892.
Advertisеment
If you are not aware about the Meltdown and Spectre vulnerabilities, we have covered them in these two articles:
- Microsoft is rolling out emergency fix for Meltdown and Spectre CPU flaws
- Here are Windows 7 and 8.1 fixes for Meltdown and Spectre CPU flaws
In short, both Meltdown and Spectre vulnerabilities allow a process to read the private data of any other process, even from outside a virtual machine. This is possible due to the implementation of how their CPUs prefetch data. Meltdown affects Intel CPUs whereas Spectre affects all CPUs. This is not some vulnerability that can only be fixed by patching the OS. The fix involves updating the OS kernel, as well as a CPU microcode update which would be done by a UEFI/BIOS/firmware update for most devices, to fully mitigate the exploits.
Recent research indicates that some ARM CPUs are affected as well by these vulnerabilities, related to speculative execution.
Microsoft has already released a set of fixes for all supported operating systems. Mozilla has issued an updated version of Firefox 57, and Google will protect Chrome users with version 64.
For the current version of Google Chrome, you can enable extra protection by enabling Full Site Isolation.
The Meltdown vulnerability and AMD CPUs
AMD CPUs are not affected by the Meltdown vulnerability. However, depending on the usage scenario, the fixes released to the operating system can cause notable performance slow down. Also, there are reports coming from AMD CPU users that the Windows patch, KB4056892 is causing serious issues for them.
While one can quickly uninstall the appropriate update package, which is KB4056892, there is also a Registry tweak you can apply to disable the Meltdown fix.
This could improve your computer's performance.
Disable the Meltdown fix on AMD CPUs
- Open the Registry Editor app.
- Go to the following Registry key.
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management
See how to go to a Registry key with one click.
- On the right, create a new 32-Bit DWORD value FeatureSettingsOverride.
Note: Even if you are running 64-bit Windows you must still create a 32-bit DWORD value.
Set its value data to 3 in decimals. - Now create a new 32-Bit DWORD value FeatureSettingsOverrideMask and set it to 3, too.
- Restart Windows 10.
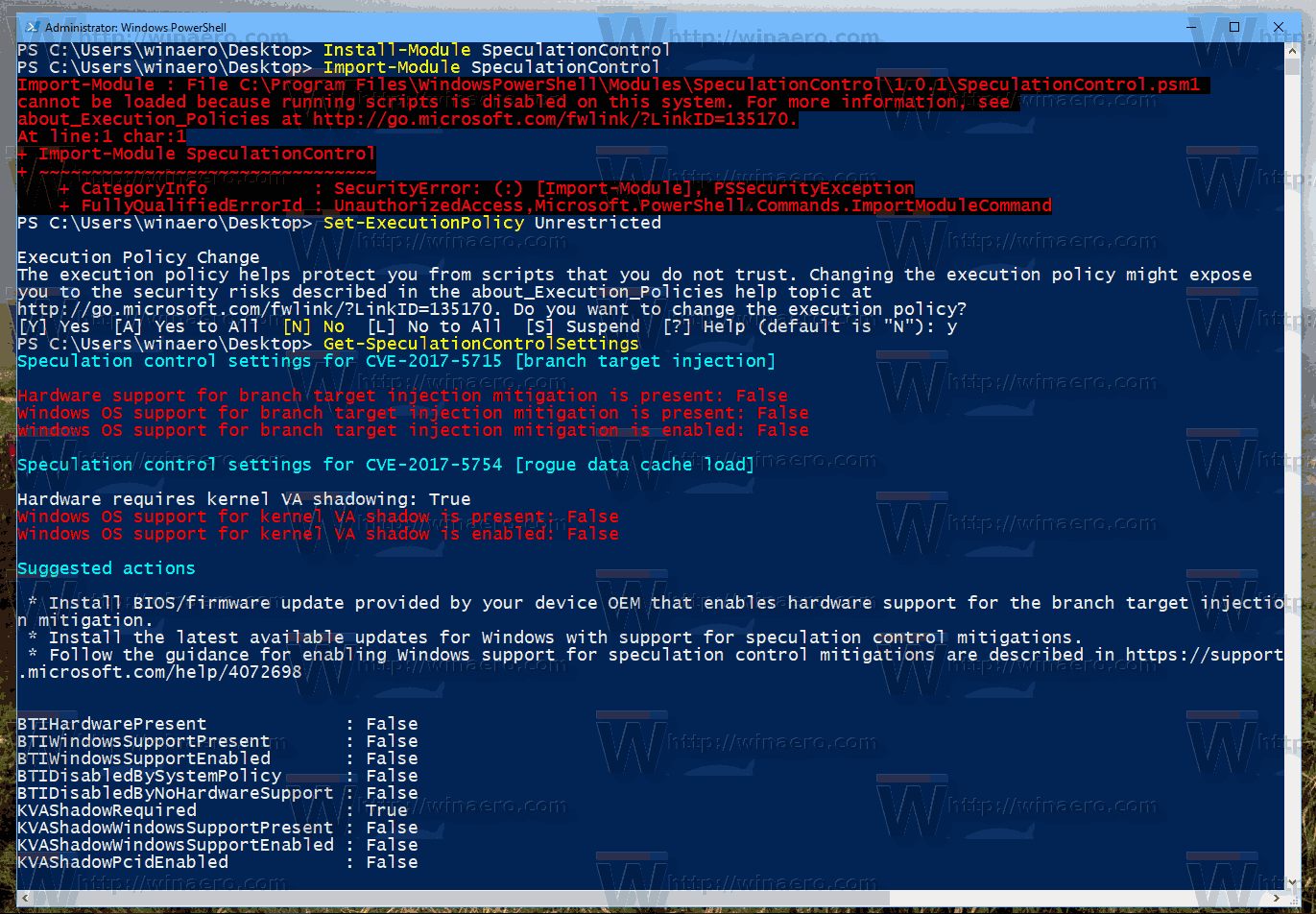
Now, you can use the PowerShell script to see the protection state as described in the article:
Find If Your PC is Affected by Meltdown and Spectre CPU Vulnerabilities
In the output, see the following lines:
Windows OS support for kernel VA shadow is present: True
Windows OS support for kernel VA shadow is enabled: False
The line "VA shadow is enabled" should be False.
That's it.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:

After KB4056892 install and reboot i have two completely dead Turion 64 X2 machine – stuck at blue Windows 10 logo and nothing. ..And not possible to boot into Safe Mode for this hotfix uninstall. Still no workable solution from AMD/Microsoft! Bigest fail till now..
Well, start the repair console from a bootable USB stick or DVD.
This might help: How to install Windows 10 from a bootable USB stick
Same for me on Athlon x2 3800+ …
This solution not working …. WU reinstall KB4056892 ….
You need to hide it in WU!
Right-click the KB4056892 line and select ‘hide’ in the context menu if you have the update in the history.
Also, Microsoft has pulled out the update from their Windows Update servers for AMD users.
It should not appear for your computer any more.
This tweak is the official solution provided by MS.
Not true. Still shows up and tries to install on my older AMD systems… fails to boot aftewards too.
Can I use this to regain performance on an Intel CPU?
I’ve not tried myself, but I think yes, you can. The code is not AMD-specific
Hi,
My PC is stuck after reboot and meltdown patch. I try this solution but… CurrentControlSet key is not existing in the hive. If I add it and the DWORD, no change, PC is not booting but the recovery is comming quicker.
Is it the good way to add the key? I load SYSTEM hive.
the way is good.
however, better try to uninstall the update. You can do something like this.
I tried this… Well, the package is in “Staged”, when I try the command I have an error : There is an exclusive session. when I try a clean-up image, its not working too, Windows is not booting
Works like a charm (i5-4690K).
it works. my pc slowed considerable the past few days.
after this registry trick it is back to normal speed. thanks
fu microsoft and fu intel
That’s really good.
I don’t know but in the windows 10 version 1709 build 16299. 229 or something like that i could able to disable the patch with the Registry tweak, but now that i upgrade to 1709 16299,547 i have all re activated… and tried the same process.. what can i do?
This is when i patched in the 1709 16299.229 was all false
https://i.imgur.com/pQZocSY.png
Then on the microsoft 1709 16299.547 build even with the registry tweak this what i got u.u
https://i.imgur.com/xqUs32t.png
What can i do? i have a ryzen 5 1600 machine.