Microsoft today revealed that in Windows 7, 8 and 10 two critical vulnerabilities exist in the font subsystem of the OS. Both of them are already exploited in "limited, targeted attacks". The company is working on a fix, and suggests a workaround.
Advertisеment
Here is the most important info about them:
- Two remote code execution vulnerabilities exist in Microsoft Windows when the Windows Adobe Type Manager Library improperly handles a specially-crafted multi-master font - Adobe Type 1 PostScript format.
- The vulnerable library ATMLIB.DLL works in kernel space.
- Windows 10 is more protected by its AppContainer/Sandbox technology.
There are multiple ways an attacker could exploit the vulnerability, such as convincing a user to open a specially crafted document or viewing it in the Windows Preview pane. To mitigate the flaw, Microsoft offers the following solutions. Note that none of them prevent an authenticated user from running a malformed document that can be used to exploit the vulnerability.
Disable WebClient Service
- Press Win+R and type
services.mscinto the Run box. - Hit Enter and find the WebClient service in the service list.
- Double click on it to open its Properties dialog.
- Change the Startup type to Disabled. If the service is running, click Stop.
Microsoft believes that this will help to exclude the remote attack vector.
There is also a workaround for the local system. It requires changing a few options for File Explorer.
Change File Explorer Options
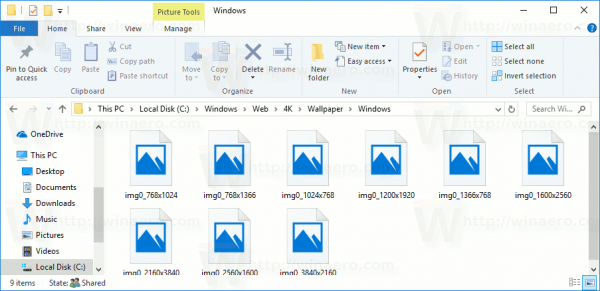
- Close all running File Explorer instances.
- Open a new File Explorer window (Win+E).
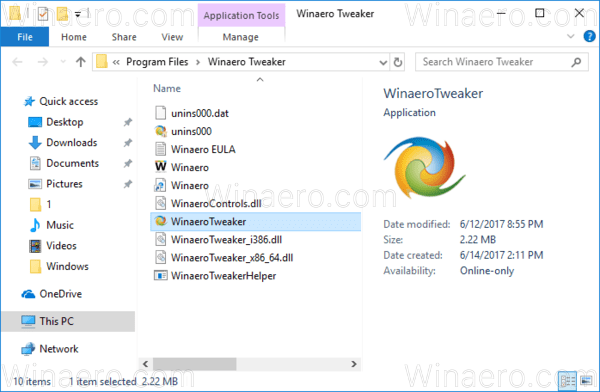
- Disable the Preview pane if you have it enabled.
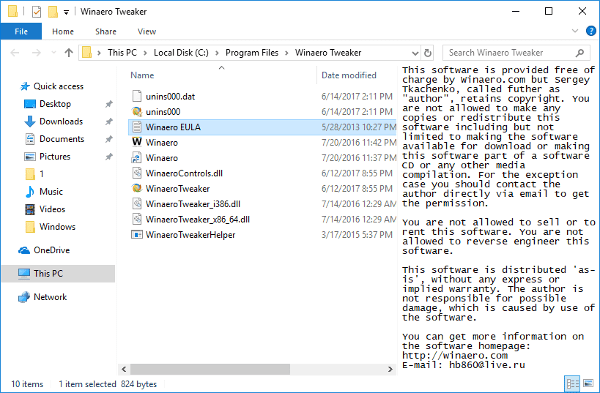
- Disable the Details pane if you have it enabled.
- Turn on "Always show icons, never thumbnails" in Folder Options.
Finally, you can disable the problematic font parser in the Registry. However, this may break certain apps that rely on that font library. Try and see if you can use Windows with it disabled until it is patched.
Disable the parser in the Registry
- Open the Registry Editor app.
- Go to the following Registry key.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows
See how to go to a Registry key with one click. - On the right, modify or create a new 32-Bit DWORD value DisableATMFD.
Note: Even if you are running 64-bit Windows you must still create a 32-bit DWORD value. - Set its value to 1.
- To make the changes done by the Registry tweak take effect, you need to restart Windows 10.
Microsoft will soon issue a fix for Windows 7, Windows 8/8.1, and Windows 10. Windows 7 users have to obtain the paid Extended Security Updates (ESU) subscription to receive it.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:

So, what does “WebClient” do anyways?
After a little searching I found” it enables me to work with web based programs and files”.
So I need it to use google docs and google calender yes?
no. they are in the browser.
Hey guys,
you say that Microsoft will soon issue a fix for Windows 7 WITHOUT paid Extended Security Updates (ESU) subscription.
But Microsoft itself states that there will NOT be a fix for Windows 7 without paid ESU – see FAQ section https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/ADV200006
Can you clarify your statement?
Thank you very much in advance!
Andreas
Hello Andreas,
Thanks for your comment.
It looks like I misread the advisory.
You are right, ESU is required.
I’ve updated the post.