Yesterday I released a new version of my freeware app, RegOwnershipEx, which is a tool for taking ownership of Registry keys and granting administrator permissions. Version 1.0.0.2 includes a few improvements and bug fixes. Here is what's new in this version.
Advertisеment
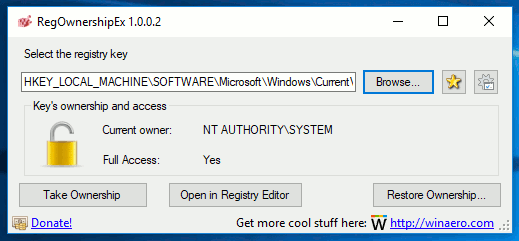
I made RegOwnershipEx to simplify the process of changing ownership of Registry keys and saving time on Registry navigation. Its two main features are:
- the ability to take ownership of a Registry key with one click (useful to get full access to the key).
- the ability to jump directly to the desired Registry key also with one click.
RegOwnershipEx features the following options:
- Take ownership and provide full access to selected Registry key.
- Restore ownership feature allows you to restore the ownership and access rights that you have changed early. i.e. this is opposite of "take ownership".
- Registry browser for easy Registry key selection.

- Favorites - for quick access to your favorite Registry locations. It is shared with Favorites menu of Registry Editor!
- Registry jump feature - you can open the selected key in Registry Editor. It is a very handy option when you read some tweaking related article and want to jump to the key mentioned in article. Simply copy-paste it into RegOwnershipEx.
- Shortcuts for root keys - you may use HKCU instead of HKEY_CURRENT_USER, HKLM instead of HKEY_LOCAL_MACHINE and so on.
- Multi language support - you will be able to translate the application into your native language by a simple ini file.
Currently, the following translations are available:
English - created by Winaero
Russian - created by Winaero
Czech - created by Milan Benes
Deutsch - created by "bildmacher"
Romanian - created by Adrian Putina
Ukrainian - created by Dmytro Zikrach
Dutch - created by "UltraWindows"
Arabic - created by "AirportsFan"
European Portuguese translation by Pedro Almeida
Swedish - created by Åke Engelbrektson.
French - created by Alain.
Hungarian - created by "BlueEyes Helpdesk".
Hebrew - created by Shai - Path Team.
Portuguese - Brazil - created by Whitewk Vx
Italian - created by Mauro Comiotto
Korean - created by Zames Dean
Danish - created by "ThomasNB"
Vietnamese - created by Tri Nguyen
Spanish - created by "FitoHB".
Chinese - created by 某宅
Polish - created by Barbara
Japanese - created by Maeda Keijiro
The Registry jump feature comes with a nice enhancement. When you open RegOwnershipEx, it analyses your clipboard content. If you copied a Registry path before launching the app, it will be pasted in RegOwnershipEx automatically!
Also, there is a useful /J command line argument. Here is how you can use it.
You can copy the path to a Registry key to the clipboard and launch the app as
RegOwnershipEx.exe /J
The Registry Editor app will be opened immediately at the path from the clipboard! This is really time saving.
Starting with version 1.0.0.2, I eliminated separate versions for x64 and x86 Windows. From now, a single executable file can be used in both x64 and x86 editions.
Another change is the ability to paste a Registry path with square brackets. You can copy such a path from a REG file and paste it in the app. It will be processed correctly. This also saves you time, since you can just copy the whole line from a REG file without editing.
Other changes are very minor. I made them mostly under the hood. Finally, this release includes an updated Czech translation.
You can download RegOwnershipEx here:
Many thanks to "moderate" who sponsored this version and performed a lot of tests before release.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
If you like this article, please share it using the buttons below. It won't take a lot from you, but it will help us grow. Thanks for your support!
Advertisеment

Thanks for the update ! Very useful little tool.
Thanks.
Thank you.
Sometimes there is not enough opportunity to become the owner of all child paths.
For example: “HKEY_LOCAL_MACHINE \ SOFTWARE \ Broadcom” has a sub-directory “HKEY_LOCAL_MACHINE \ SOFTWARE \ Broadcom \ 802.11”. Then, when requesting rights to the first path, you can access all nested directories.
Sometimes, you get the path to one path, but inside there are a few more ways with a multiple nesting of paths. For example: “HKEY_LOCAL_MACHINE \ SOFTWARE \ Broadcom \ 802.11 \ x8447 \ right”.
–
In connection with the written, I would like a recursive analysis of all nested directories with access to each. Only, after gaining access to one, to check new names opened and to check access to them.
–
A case, extremely. Not frequent, therefore, please make the function a separate item of settings. With the question “do I have access to all child paths?”
———-
Спасибо.
Иногда не хватает возможности стать владельцем всех дочерних путей.
Например: “HKEY_LOCAL_MACHINE\SOFTWARE\Broadcom” имеет субдерректорию “HKEY_LOCAL_MACHINE\SOFTWARE\Broadcom\802.11”. Тогда, при запросе прав на первый путь, получать доступ ко всем вложенным дирректориям.
Бывает, получаешь путь к одному пути, а внутри ещё несколько путей с неоднократным вложением путей. Например: “HKEY_LOCAL_MACHINE\SOFTWARE\Broadcom\802.11\x8447\right”.
—
В связи с написанным, хотелось бы рекурсивный анализ всех вложенных дирректорий с получением доступа к каждой. Только, после получения доступа к одной, проверять открылись новые наименования и проверять доступ к ним.
—
Случай, крайне. не частый, поэтому, просьба сделать функцию отдельным пунктом настроек. С вопросом “получить доступ ко всем дочерним путям?”
I will do. This is one of most requested features.
Сделаем. Эту функцию часто просят реализовать.
listed in CodeProject’s ‘Free Tools” forum:
https://www.codeproject.com/Messages/5379620/freeware-registry-app-RegOwnershipEx-new-version.aspx
cheers, Bill
Thanks!
Hi,
I tested your tool on Win10 / RS2 / v1703 / Build 15063.11.
Unfortunatly I can’t get access to
– [HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions\Paths]
in order to insert keys like
– „C:\\P\\N_LAUNCH“=dword:00000000
– „C:\\P\\UTIL“=dword:00000000
although your tool and “Properties|Security” report “Full Rights” for Administrators
I hope you’ll find a way to make it work like on RS1 and before.
Regards, Nemo
This is because that path is protected by the Defender’s realtime driver.
Hi Sergey,
Any idea hwo to solve the problem?
Regards, Nemo
Try to disable defender first.
See these articles:
How to Disable Windows Defender
Disable Early Anti-malware launch