Microsoft is on a way to deprecate a Registry option that disables Microsoft Defender's antivirus engine. The company will continue to provide the Group Policy and the corresponding Registry tweak for that Policy, but the client option will be ignored in Home and Pro editions of the OS.
Advertisеment
Windows Defender is the default antivirus app shipped with Windows 10. Earlier versions of Windows like Windows 8.1, Windows 8, Windows 7 and Vista also had it but it was less efficient previously as it only scanned spyware and adware. In Windows 8 and Windows 10, Defender is based on the Microsoft Security Essentials app which offers better protection by adding full blown protection against all kinds of malware. Microsoft is renaming the app Microsoft Defender.

Recent Windows 10 version come with is a new app called Windows Security. The application, formerly known as "Windows Defender Dashboard" and "Windows Defender Security Center", has been created to help the user control his security and privacy settings in a clear and useful way. It includes all the settings related to Windows Defender. The Security Center app is reviewed in the post Windows Defender Security Center in Windows 10 Creators Update.
Defender signature updates are tied to the built-in Windows Update feature. In older Windows 10 releases, when you have it disabled, paused with Focus Assist, or you are on a metered connection, Microsoft Defender couldn't receive signature updates. In this case, you could use a number of methods to manually update Defender signatures:
- Manually Update Definitions for Windows Defender in Windows 10
- Schedule Defender Signature Updates in Windows 10
Starting in Windows 10 build 20175, Microsoft implemented a new Group policy that allows enabling updates for Microsoft Defender without extra hacks.
Deprecation of the DisableAntiSpyware parameter
DisableAntiSpyware is a special option in the Registry and PowerShell that can be used to disable Defender. It is available in all editions of Windows 10, including Home and Pro. Microsoft is changing that, as noticed by Deskmodder.
This setting is discontinued and will be ignored on client devices, as of the August 2020 (version 4.18.2007.8) update to Microsoft Defender Antivirus.
Advanced users and administrators still can use the Group Policy and related options to disable Defender.
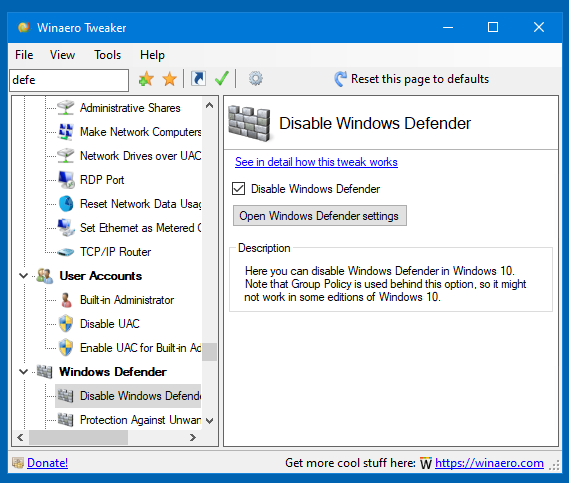
There are a number of freeware tools that you can use to save your time, including Winaero Tweaker, that will help you to disable it.
Finally, installing an alternative anti-virus solution will disable Microsoft Defender.
It is not a secret that Microsoft is not interested in users disabling the Defender antivirus, so the company may apply further restrictions, and remove or limit the use of the Group Policy option to certain editions of the OS, leaving consumers without any option to permanently disable the app.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:

Would it still be possible to disable Microsoft Defender antivirus completely using Group Policy?
Yep. At least for now.
I know it’s in the winaero screenshot but I just want to confirm from the author – so as long as I have been using that checkbox in winaero to disable Defender, that is all I need to do and it’s confirmed that it’s still being disabled? I’m using Win 10 Pro so I have the ability to modify group policy and it’s been working so far.
In recent Windows 10 versions Microsoft has enabled Tamper protection. To be able to turn on the checkbox, it needs to be disabled first. The app will show you a warning that the Tamper Protection is preventing it from modifying Defender’s policies.
Now, Malwarebytes started to flag Winaerotweaker as virus e deleted it from my computer, I had to create an exclusion on MBAM options to be enable to reinstal winaerotweaker again.
This article makes no sense. The group policy and registry setting is the same thing (all gpedit does is apply it to the registry for you) therefore if gpedit works, then the registry edit will still work as well. I’ve checked the policy still works in 20h2 and ironically, tends to work best if you apply it to the registry manually instead of getting gpedit to do it for you. Therefore its the opposite way round to what is written here. Sadly, it doesn’t seem to work at all in 21h1. The original documentation also said that the depreciation would only apply to Windows 10 pre-1903, which was the version that started to use the Tamper Protection feature, and is now an unsupported version anyway.