Attackers use AppInstaller.exe on Windows to distribute the BazarBackdoor malware. That has been found by Cybersecurity researchers at Sophos Labs. A new phishing attack is being used to spread the malware.
Interestingly, the Sophos Labs employees themselves were targets of the email spam attack.
In one of the email messages allegedly sent by a “Sophos Main Manager,” Adam Williams, who doesn't actually exist. "He" wondered why the researcher had not responded to a client's complaint.
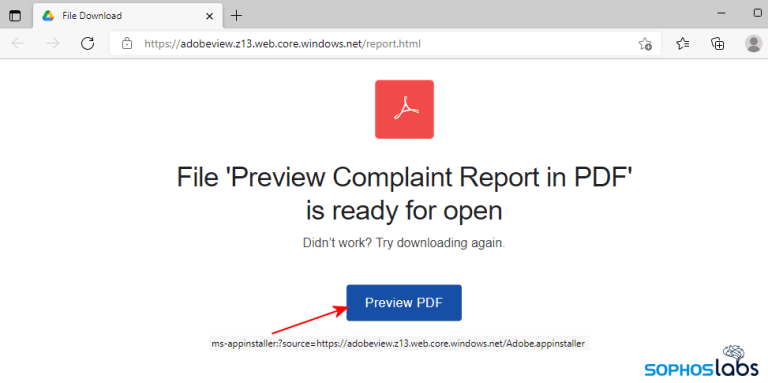
The email included a link to a PDF message that revealed a new malware distribution method. It involves the Microsoft App Installer used by the Store app in Windows 10 and Windows 11.
The URL begins with the ms-appinstaller:// protocol. Clicking on the link will launch the default browser, say Microsoft Edge, which will subsequently launch the AppInstaller.exe software used by the Microsoft Store to install applications.
The link points to a text file called Adobe.appinstaller, which contains the instructions to download and install a file called Adobe_1.7.0.0_x64.appbundle. The software is signed with a certificate that was issued just a few months ago, by Systems Accounting Limited, based in the UK.
The installer will prompt the user to install a software called "Adobe PDF Component". If permission is granted, the BazarBackdoor malware will be downloaded and launched on the system in seconds.
BazarBackdoor, like BazarLoader, communicates over HTTPS, but differs from it in the large amount of noisy traffic that the backdoor generates. BazarBackdoor is known to intercept system data. It is also believed to be related to the installation of Trickbot and the Ryuk ransomware.
More details can be found on the official Sophos blog.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
