VBA (Visual Basic Application) macros in Office apps are a pain for many IT Admins and regular users. Hackers often use VBA macros to infect typical Office documents and target people to steal sensitive data, spread malware, remote access, and do other sorts of nasty things. Usually, opening an infected Office document from an email attachment is all it takes to get in trouble. Microsoft now wants to fix this problem for good.
Advertisеment
This is not the first time Microsoft has attempted to fix the problem of infected Office documents. Microsoft Office apps block macros in documents from untrusted sources by default, but users can run VBA with a single click on the toolbar. Soon, Microsoft will ditch that button and make enabling VBA in downloaded Office files much harder.
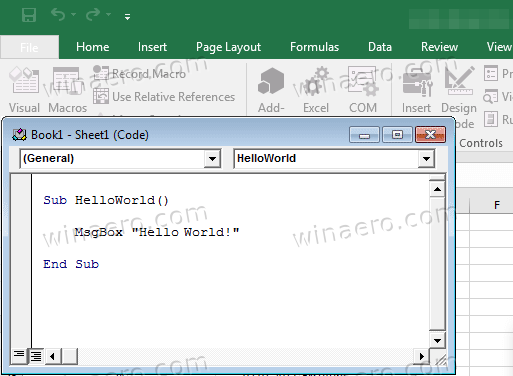
Future Office updates will delete the button that lets you enable VBA in downloaded Office files. Once the user opens a file with attached macros, Office will show a "Security Risk" message without an apparent override button. The warning links to a support article that describes the dangers of using VBA macros in files downloaded from the Internet. Also, it tells how to enable VBA if the user trusts the file source.
"Security Risk. Microsoft has blocked macros from running because the source of this file is untrusted."
Microsoft plans to add the new VBA warning to the following Office apps: Access, Excel, PowerPoint, Visio, and Word. The change will first arrive for Microsoft 365 subscribers in version 2203 in early April 2022 (in the Current Channel first). Later on, Microsoft will update Office LTSC, Office 2021, Office 2019, Office 2016, and even Office 2013.
You can learn more about how Microsoft plans to protect Office users from malicious VBA macros in a post on the Tech Community forums.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
