Although the concept of multiple users sharing one device or one PC is getting rarer by the day, there are still cases when you have to share PCs. In such a situation, it is useful to have multiple user accounts on a single PC. In Windows 10, it is possible to prevent specific user accounts or members of a group from signing in to the operating system locally.
Advertisеment

By default, normal user accounts created in Windows 10 are configured for signing in locally. When Windows 10 starts, it shows you a login screen and prompts you for a password. If you have more than one user account in your OS, you will be able to click the user image of the account you want and then enter the account password.
Note: Specific user accounts can be hidden from the login screen. Windows 10 can be configured to ask for a user name and password.
It is possible to entirely prevent users or a group from logging on locally. There's a security policy that determines which users are prevented from logging on directly at the device's console. Here is how to set it.
Warning: If you apply this policy setting to the Everyone group, no one will be able to log on locally.
If you are running Windows 10 Pro, Enterprise, or Education edition, you can use the Local Security Policy app to deny a user or group from logging on locally. All Windows 10 editions can use an alternative method mentioned below.
To Deny Sign in User or Group to Sign in Locally in Windows 10,
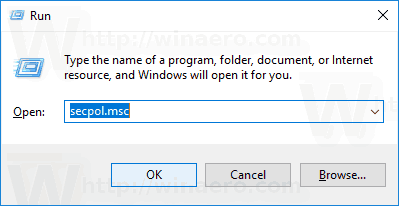
- Press Win + R keys together on your keyboard and type:
secpol.msc
Press Enter.
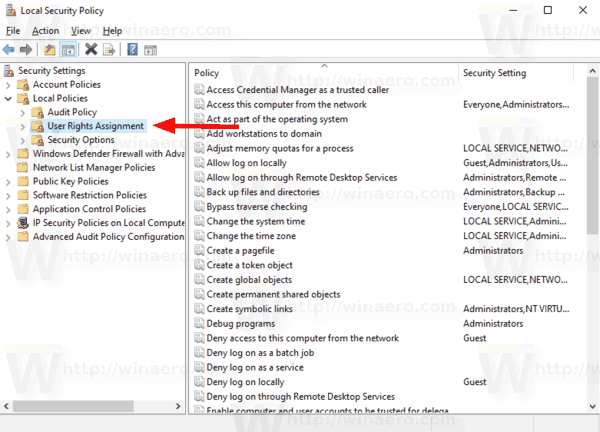
- Local Security Policy will open. Go to User Local Policies -> User Rights Assignment.
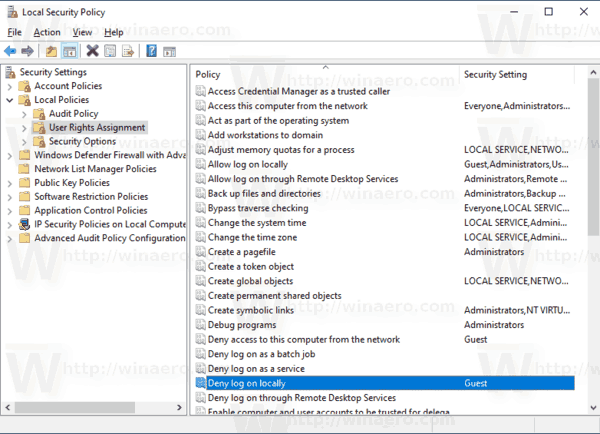
- On the right, double-click on the policy Deny log on locally to change it.
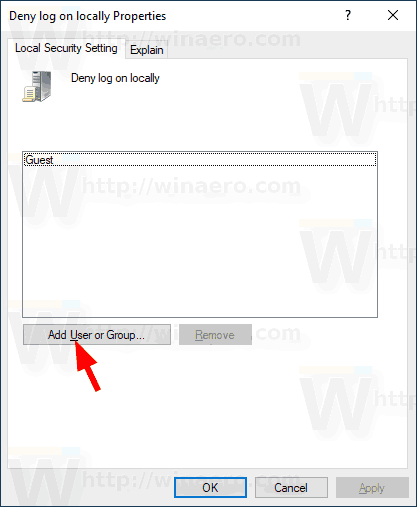
- In the next dialog, click Add User or Group.
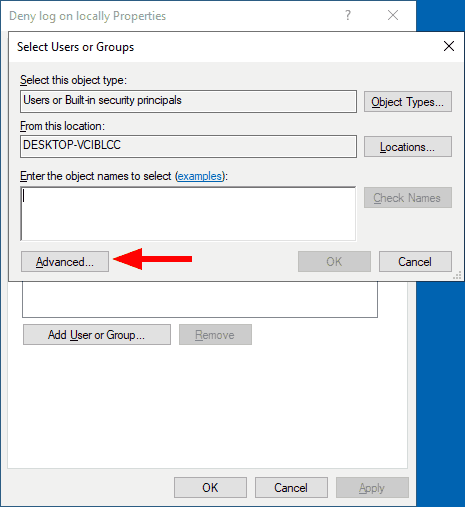
- Click on the Advanced button.
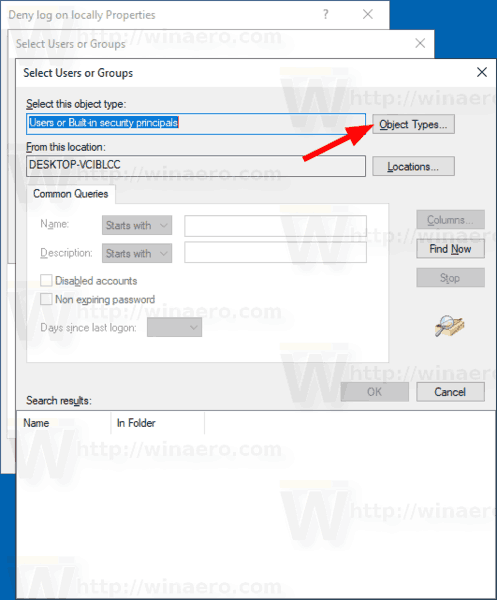
- Now, click on the Object Types button.
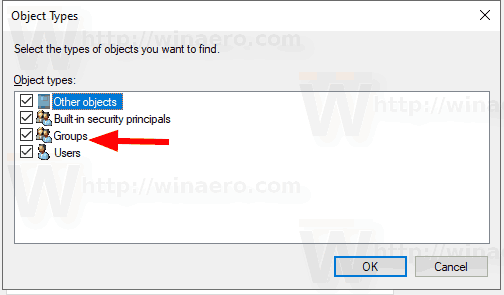
- Ensure that you have the Users and Groups items checked and click on the OK button.
- Click on the Find now button.
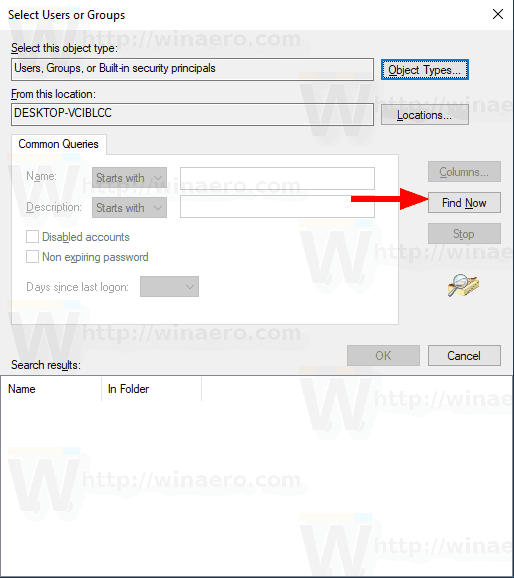
- From the list, select the user account or group to deny log on locally for it. You can select more than one entry at once by holding the Shift or Ctrl keys and clicking on the items the list.
- Click on the OK button to add the selected items to the Object names box.
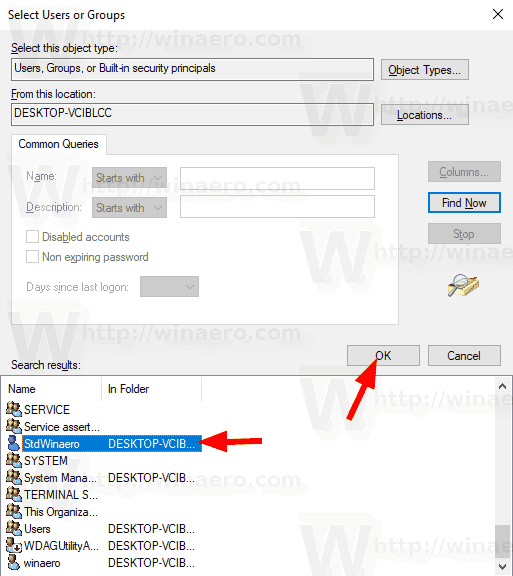
- Click on the OK button to add the selected items to the policy list.
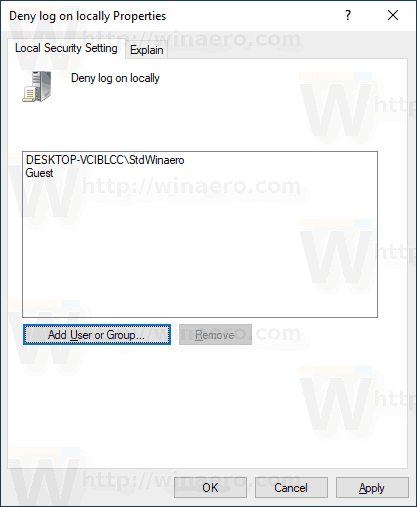
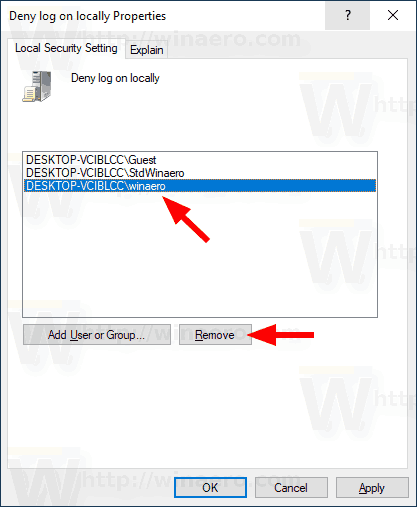
- To remove any added entry, use the Remove button in the policy dialog.
You are done.
If your Windows edition doesn't include the secpol.msc tool, you can use the ntrights.exe tool from Windows 2003 Resource Kit. Many resource kit tools released for previous Windows versions will run successfully on Windows 10. ntrights.exe is one of them.
The ntrights tool
The ntrights tool allows you to edit user account privileges from the command prompt. It is a console tool with the following syntax.
- Grant a right:
ntrights +r Right -u UserOrGroup [-m \\Computer] [-e Entry] - Revoke a right:
ntrights -r Right -u UserOrGroup [-m \\Computer] [-e Entry]
The tool supports plenty of privileges which can be assigned to or revoked from a user account or group. Privileges are case sensitive. To learn more about the supported privileges, type ntrights /?.
To add ntrights.exe to Windows 10, read this post: What is the ntrights app and how you can use it. You can place the ntrights.exe file to the C:\Windows\System32 folder to quickly call it.
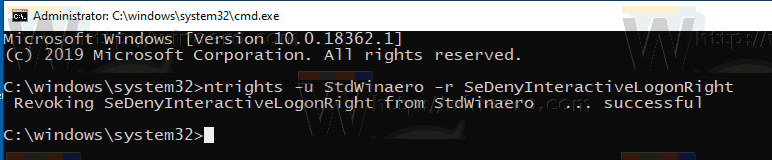
Deny log on locally with ntrights
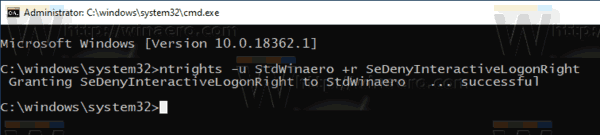
- Open an elevated command prompt.
- Type the following command to deny local logon right:
ntrights -u SomeUserName +r SeDenyInteractiveLogonRight
Substitute the SomeUserName portion with the actual user name or group name. The specified user will be prevented from locally signing to Windows 10.
- To undo the change and allow the user to log on locally, execute
ntrights -u SomeUserName -r SeDenyInteractiveLogonRight
That's it.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
