How to exclude an app from Untrusted Font Blocking in Windows 10
If you have enabled the Untrusted Font Blocking feature, you might want to exclude specific apps from being blocked when loading a font. It can a be a trusted app, or an app you need which fails to work properly under the restrictions you have set. Here is how it can be done.
Advertisеment
Windows 10 comes with TrueType fonts and OpenType fonts installed out-of-the-box. They either have TTF or OTF file extensions. They support scaling and look sharp on modern displays.
You may be familiar with the classic Fonts Control Panel applet, which you could use to see the fonts that are currently installed, or to install or uninstall fonts.
Starting with build 17083, Windows 10 features a special section in the Settings app. The new section, called simply "Fonts", can be found under Personalization.
Instead of the classic applet, recent releases of Windows 10 offer the Fonts page in Settings, which is able to show off newer font capabilities, such as color fonts or variable fonts. A refresh of the Fonts UI to show off the newer capabilities was long overdue.
In Settings, a dedicated page for Fonts settings provides a short preview of each font family. The previews use a variety of interesting strings that are selected to match the primary languages that each font family is designed for, together with your own language settings. And if a font has multi-color capabilities built into it, then the preview will demonstrate this.
The OS comes with an advanced security feature that prevents fonts from being loaded outside of the c:\Windows\Fonts folder, considering them untrusted.
Untrusted Font Blocking in Windows 10
The Untrusted Font Blocking security feature in Windows 10 is implemented as a global option that prevents apps from loading untrusted fonts. When enabled, any font that is located outside of the C:\Windows\Fonts folder, considered untrusted. This option can be set to one of the following values: On, Off, and Audit. You can configure it with a Group Policy (where available), or by applying a Registry tweak.
There are 3 ways to use this feature:
- On. Helps stop any font processed using GDI from loading outside of the
%windir%/Fontsdirectory. It also turns on event logging. - Audit. Turns on event logging, but doesn’t block fonts from loading, regardless of location. The name of the apps that use untrusted fonts appear in your event log.
- Exclude apps to load untrusted fonts. You can exclude specific apps, allowing them to load untrusted fonts, even while this feature is turned on.
Here is how you can exclude apps from being blocked when loading untrusted fonts.
To Exclude App from Untrusted Font Blocking in Windows 10,
- In Event Viewer, find the log record for the app you want to exclude.
- Note the executable file name for the app, e.g.
iexplore.exefor Internet Explorer.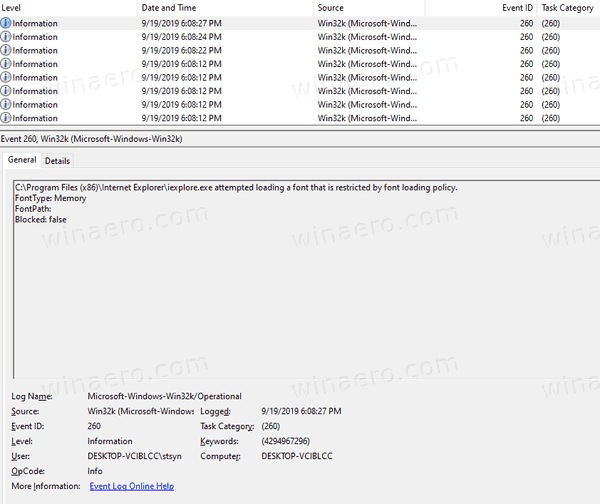
- Open the Registry Editor app.
- Go to the following Registry key.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options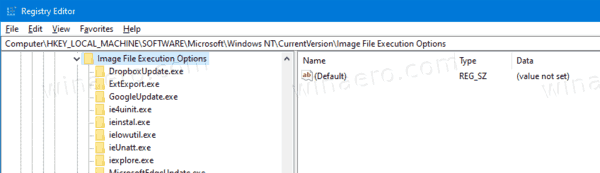
See how to go to a Registry key with one click. - See if you have a subkey named after the app's name (e.g.
iexplore.exefor Internet Explorer) under Image File Execution Options. If it doesn't exist, then create it.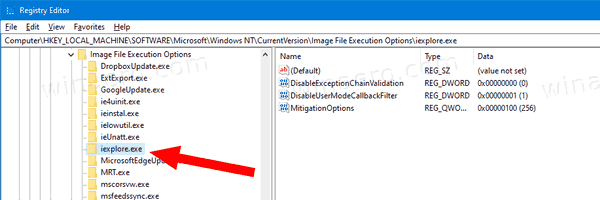
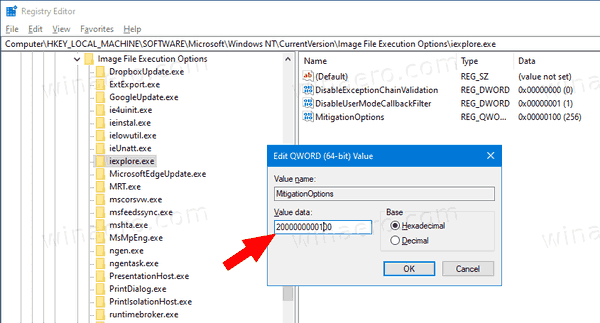
- On the right of the executable file name key (e.g. iexplore.exe), modify or create a new QWORD (64-bit) value MitigationOptions.
- Set its value in Hexadecimal to 2000000000000 to exclude the app. See the note below.
- Restart Windows 10.
That's it.
Note: Other values you can set for MitigationOptions.
-
1000000000000. Block untrusted fonts for this app and log its events. -
2000000000000. Exclude the app from being blocked. -
3000000000000. Enables Audit mode. Do not block untrusted fonts for the app, but write its events to the log.
Important! Your existing MitigationOptions values should be saved during your update. For example, if the current value is 1000, your updated value should be 1000000001000.
Related articles:
- Enable or Disable Untrusted Font Blocking in Windows 10
- Read Event Viewer Log for Untrusted Font Blocking in Windows 10
- Backup and Restore Font Settings in Windows 10
- Delete and Uninstall a Font in Windows 10
- How To Rebuild Font Cache in Windows 10
- Change ClearType Font Settings in Windows 10
- How to Install Fonts in Windows 10
- How To Install Fonts From Microsoft Store In Windows 10
- How to a Hide a Font in Windows 10
- Hide a Font Based on Language Settings in Windows 10
- Restore Default Font Settings in Windows 10
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
