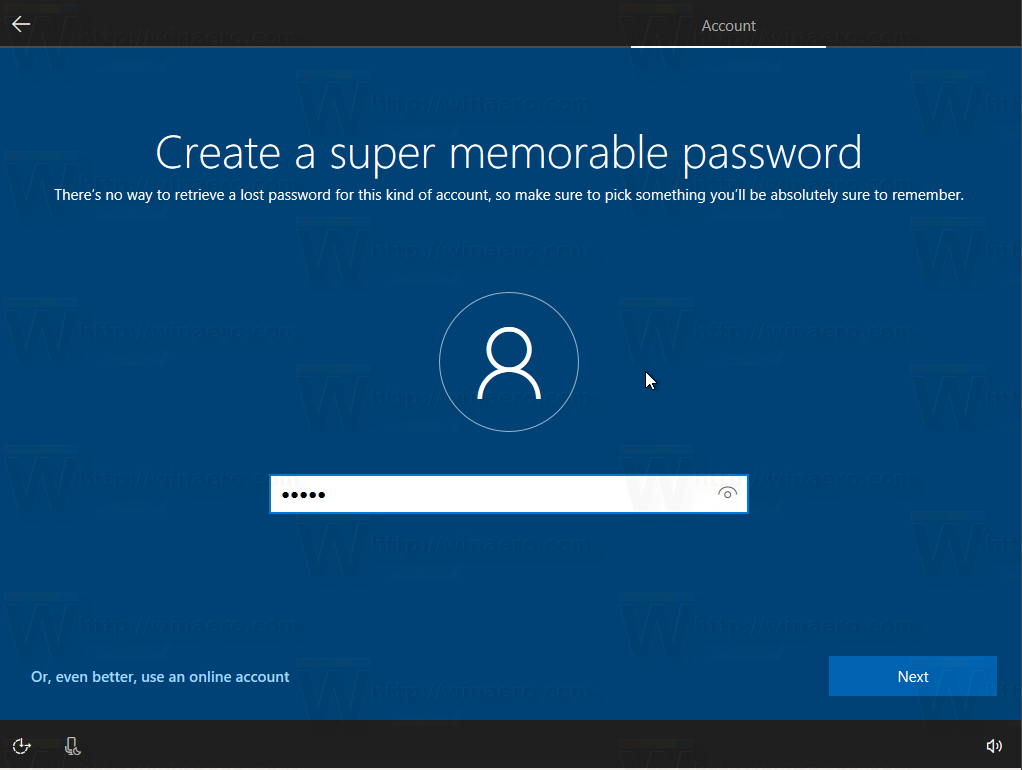
Windows 10 supports two types of accounts. One is the classic local account which has been available in all previous Windows versions, the other one is the modern Microsoft Account which is connected with the company's cloud services. Prior to Windows 10 version 1903, Microsoft had configurable password expiration policies for better security dating back to the earliest versions of Windows NT. This has changed.
Advertisеment
In short, Microsoft now has the following arguments against continuous password changing.
- If a password has got compromised, it should be changed right away.
- If a password wasn't compromised, there is no reason to change it.
- Periodical password changing can make users forget their new password, or make them write it down somewhere where the password can be easily spotted.
The official blog post states the following.
Why are we removing password-expiration policies?
First, to try to avoid inevitable misunderstandings, we are talking here only about removing password-expiration policies – we are not proposing changing requirements for minimum password length, history, or complexity.
Periodic password expiration is a defense only against the probability that a password (or hash) will be stolen during its validity interval and will be used by an unauthorized entity. If a password is never stolen, there’s no need to expire it. And if you have evidence that a password has been stolen, you would presumably act immediately rather than wait for expiration to fix the problem.
If it’s a given that a password is likely to be stolen, how many days is an acceptable length of time to continue to allow the thief to use that stolen password? The Windows default is 42 days. Doesn’t that seem like a ridiculously long time? Well, it is, and yet our current baseline says 60 days – and used to say 90 days – because forcing frequent expiration introduces its own problems. And if it’s not a given that passwords will be stolen, you acquire those problems for no benefit. Further, if your users are the kind who are willing to answer surveys in the parking lot that exchange a candy bar for their passwords, no password expiration policy will help you.
Our baselines are intended to be usable with minimal if any modification by most well-managed, security-conscious enterprises. They are also intended to serve as guidance for auditors. So, what should the recommended expiration period be? If an organization has successfully implemented banned-password lists, multi-factor authentication, detection of password-guessing attacks, and detection of anomalous logon attempts, do they need any periodic password expiration? And if they haven’t implemented modern mitigations, how much protection will they really gain from password expiration?
The results of baseline compliance scans are usually measured by how many settings are out of compliance: “How much red do we have on the chart?” It is not unusual for organizations during audit to treat compliance numbers as more important than real-world security. If a baseline recommends 60 days and an organization with advanced protections opts for 365 days – or no expiration at all – they will get dinged in an audit unnecessarily and might be compelled to adhere to the 60-day recommendation.
Periodic password expiration is an ancient and obsolete mitigation of very low value, and we don’t believe it’s worthwhile for our baseline to enforce any specific value. By removing it from our baseline rather than recommending a particular value or no expiration, organizations can choose whatever best suits their perceived needs without contradicting our guidance. At the same time, we must reiterate that we strongly recommend additional protections even though they cannot be expressed in our baselines.
So, the password expiration policies are deprecated starting in Windows 10 version 1903. This change doesn't affect other password policies, including the policies for length and complexity.
You can review the changes here: Security baseline (DRAFT) for Windows 10 v1903 and Windows Server v1903
See the following articles:
- Reset Windows 10 password without using third party tools
- All ways to change the user password in Windows 10
- How to Use Password-less Accounts to Sign-in to Windows 10
- Prevent Windows 10 from Syncing Passwords Between Devices
- Prevent User From Changing Password in Windows 10
- How to Remove the User Password in Windows 10
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:

About damn time I say. It’s especially annoying if you’re on a domain joined machine, working away from office and your company has no VPN, forcing you to come in to the office just to change your password.
Yep, that’s true. I had the same issue multiple times.
it’s not a pb when you are using Azure AD
No need to have a VPN
That is what really was need it for Windows 10 to be better ???
It look for me that someone try to justify their salary by “fixing” things that don’t really need to be fixed
Oh, boy
That sound for me like opening a new Pandora box or sound like trading a devil we know for one that we don’t (or that is worst than the previous devil)
In practice is very useful and healthy to periodic change passwords , in special in the work / business environment . It has less issues .
Imagine a bad employ that was fired , still having access to some of the company systems because nobody changed the passwords periodically .
Changing the passwords periodically is not perfect , had it’s issues .
But from security and legislation point of view and who is responsible , changed the passwords periodically is the way to go .
Imagine a bad person defending himself that the only way he was able to access those systems is because nobody changed the passwords periodically.
Who will be responsible for us to sue if our data will be compromise because a company (like Amazon) got “hacked” because the “hacker” got access by using the passwords that he obtain many months previous the attack (passwords that was still valid because nobody changed the passwords periodically) .
I think it will common guild , but non the last , a legislative nightmare
Does this affect those who using Windows server 2012 as a domain controller and got clients running windows 10 1903?
No, it should not affect.