There is a long-standing bug in Windows that damages the file system with a variety of actions. A single command, a malformed HTML file, or even a shortcut that you see in a ZIP archive can corrupt the file system. Windows 10, starting with version 1803, and reportedly Windows 8/8.1 are among the vulnerable operating systems.
Advertisеment
A security researcher, Jonas L, discovered an NTFS vulnerability impacting Windows 10 that has not been fixed yet. The researcher told BleepingComputer that the flaw became exploitable starting around Windows 10 build 1803, the Windows 10 April 2018 Update, and continues to work in the latest version. I've heard that Windows 8 and Windows 8.1 are also affected by the issue, and even Windows XP. But Windows 7 is not affected. This is as per other people's reports. Winaero has not verified older systems themselves.
How it works
The issue is really serious. A simple command, even when executed by a low privileged user, corrupts an NTFS-formatted hard drive, with Windows prompting the user to restart their computer to repair the corrupted disk records.
Warning: Do not test this command on any of your devices containing important data. The file system will be damaged, and you may lose all your data. You have been warned.
The command looks as follows.
![]()
The key thing here is the $i30 NTFS index attribute. That NTFS Index Attribute is an attribute associated with directories that contains a list of a directory's files and subfolders. In some cases, the NTFS Index can also include deleted files and folders.
'I have no idea why it corrupts stuff and it would be a lot of work to find out because the reg key that should BSOD on corruption does not work. So, I'll leave it to the people with the source code,'
... the researcher said.
The above command can corrupt any drive, not only the C: drive. After you hit Enter, an error message will appear stating "The file or directory is corrupted and unreadable."
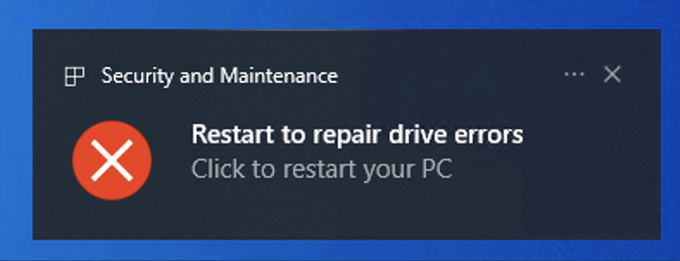
Windows 10 will prompt the user to restart the computer in order to repair the corrupted drive. On reboot, the Windows CheckDisk app will start and fix the file system.
It can be triggered by a variety of methods
It is not only the above command that causes the issue. A specially prepared Internet shortcut file (.url) that had its icon location set to C:\:$i30:$bitmap will trigger the vulnerability even if the user never opened the file. Once File Explorer attempts to display such an "icon", the drive will instantly become corrupted. All you need to do is to view it in File Explorer.
If such a file is included in a ZIP archive, that ZIP archive will trigger the vulnerability every single time it is extracted. Similarly, it can be placed in an ISO, VHD or VHDX file.
The researcher said that a crafted HTML page that embeds resources from a network share will do the same.
Finally, users have figured that it is enough to paste the above ':$i30' string into the browser address bar.
The fix is being worked upon
The Verge has contacted Microsoft, and the company's spokesperson has ensured that they are already working on a fix for this issue.
We are aware of this issue and will provide an update in a future release. The use of this technique relies on social engineering and as always we encourage our customers to practice good computing habits online, including exercising caution when opening unknown files, or accepting file transfers.
So, there is no mitigation for this vulnerability as of this writing. Be careful while downloading and viewing files. If you suspect any threat, use a console file manager like Far that doesn't display and retrieve icons.
Support us
Winaero greatly relies on your support. You can help the site keep bringing you interesting and useful content and software by using these options:
If you like this article, please share it using the buttons below. It won't take a lot from you, but it will help us grow. Thanks for your support!
Advertisеment

Nice to know Microsoft are on the ball as usual
Why does everyone write that it corrupts ur data? Because it doesnt. I tried this and my pc worked just fine.
According to Bleeping Computer, several users ended up with a RAW partition. It will be hard to get it back, as chkdsk won’t help.
A simple chkdsk utility is gonna make the disc completely fine
目前来看应该是无害的,因为你用.bat写入start cd C:\:$i30:$bitmap是没有反应的(这时Windows安全中心显示是特洛伊木马“Trojan:Win32/MaftaCorrupter.A”)重启也不需要扫描磁盘